
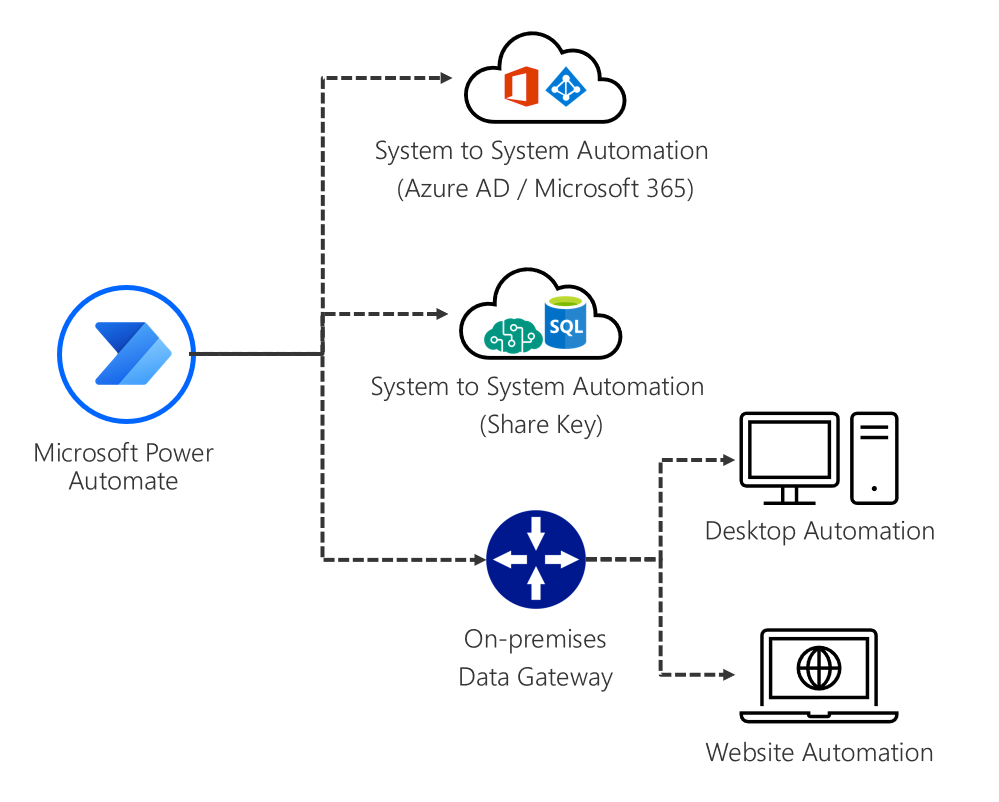
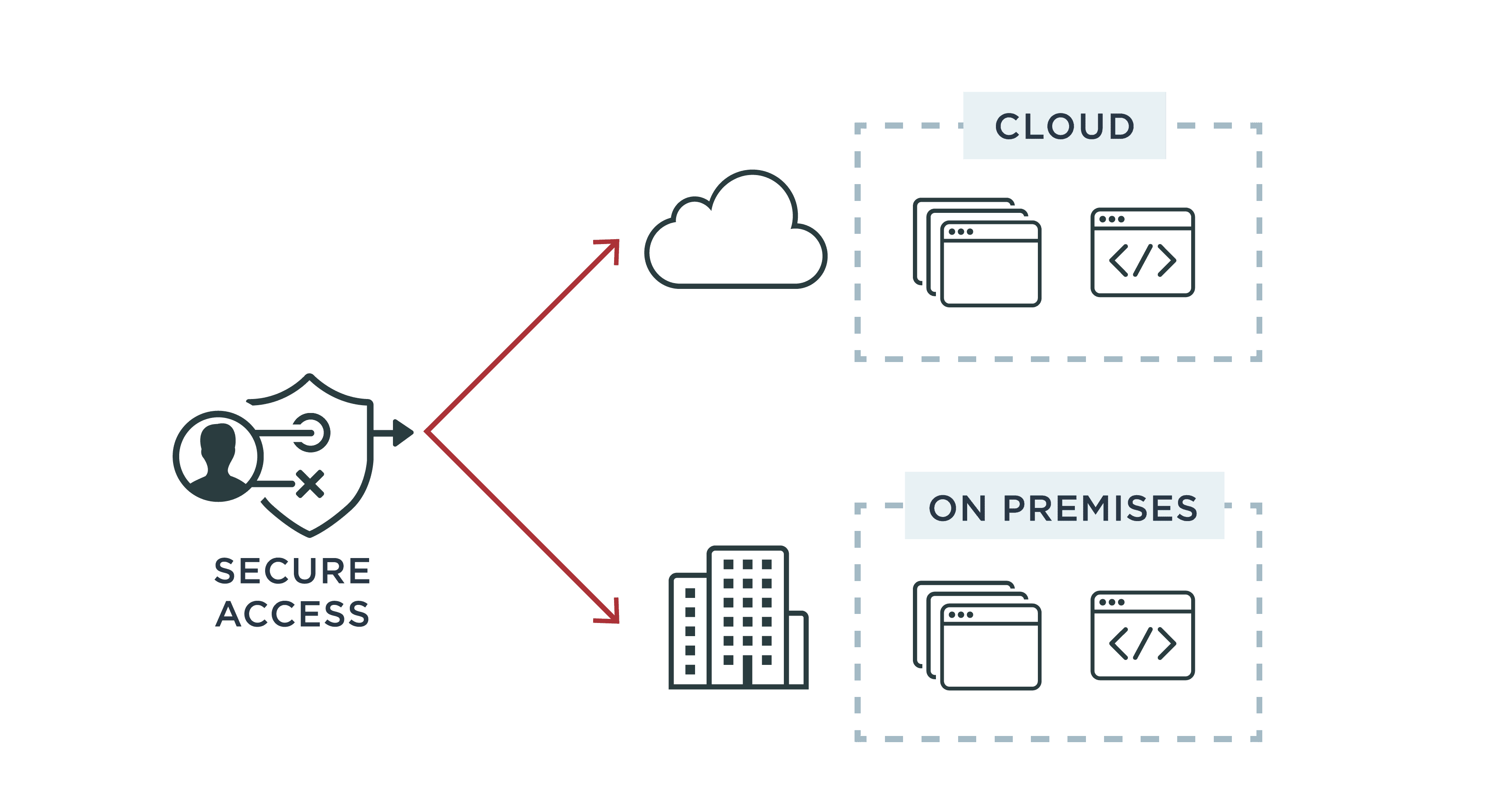
The Hidden Costs of DIY Cloud Data Lakes #2: Identity Management and Authentication (Single Sign-On) - Cazena | Cazena

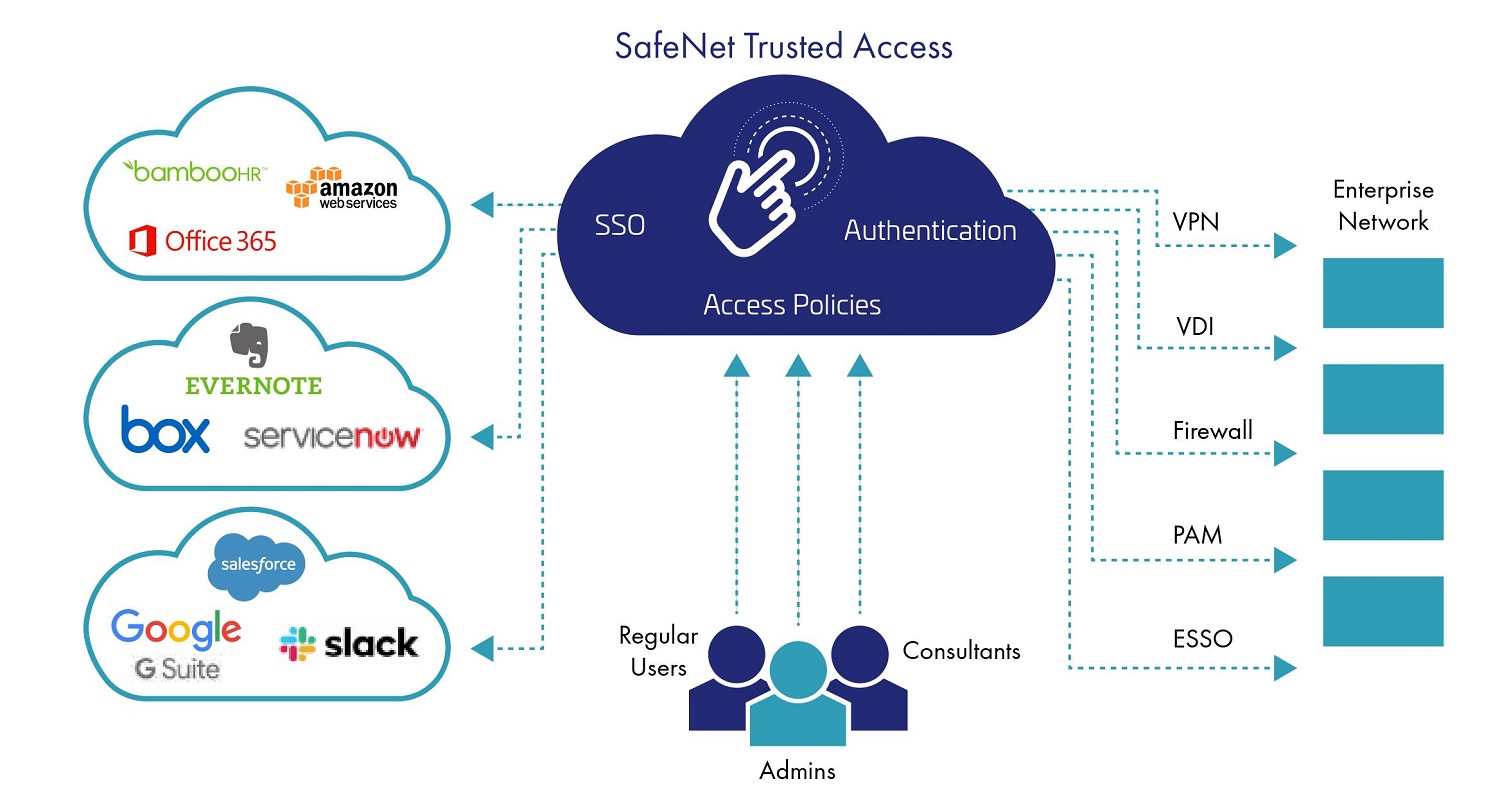
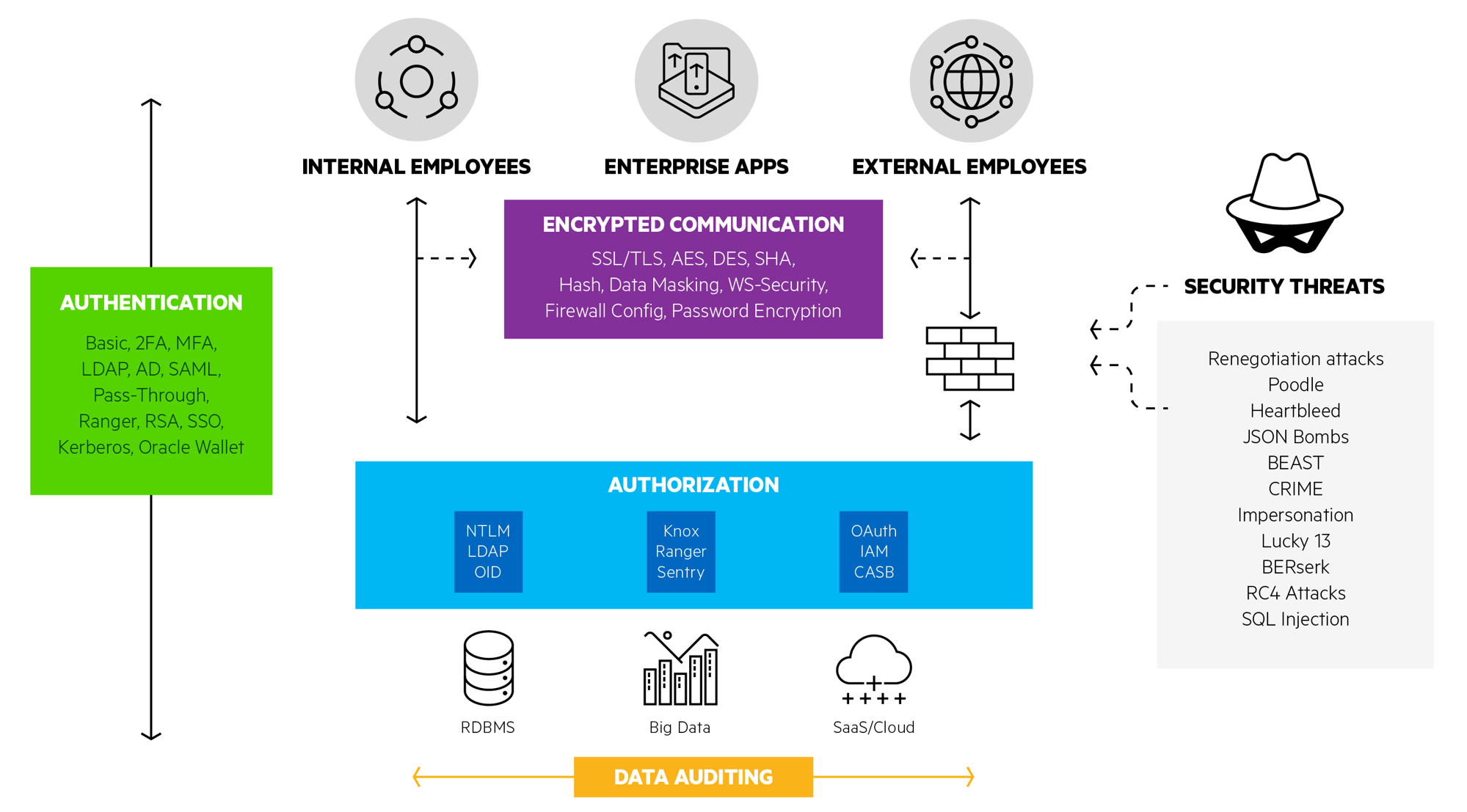
Encryption and Authentication: The One-Two Punch That Protects Your Data | 2019-07-02 | Security Magazine
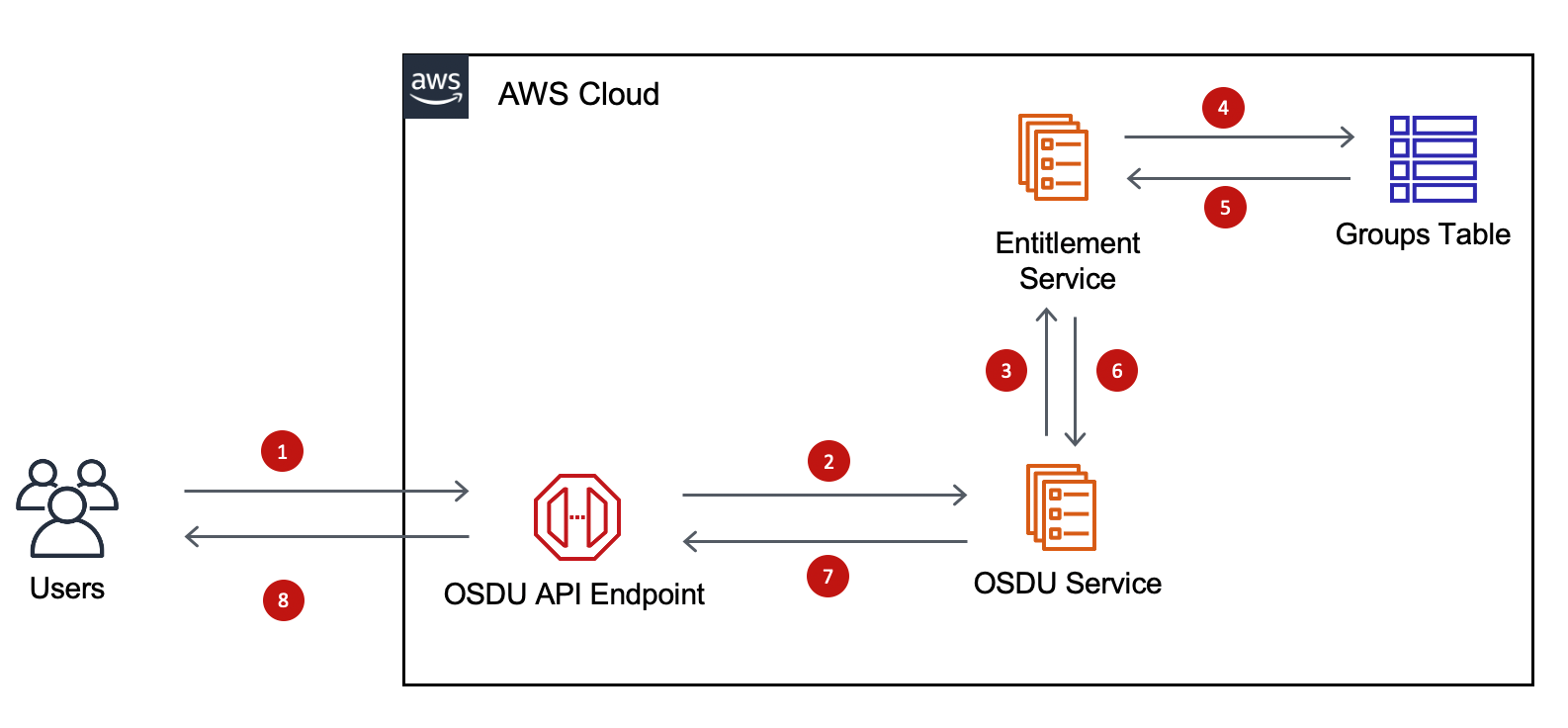
Subsurface Data Management: Overview of authentication and authorization on AWS implementation of OSDU™ Data Platform | AWS for Industries








![MS-AUTHSOD]: Data Origin Authentication (Signing) | Microsoft Learn MS-AUTHSOD]: Data Origin Authentication (Signing) | Microsoft Learn](https://learn.microsoft.com/en-us/openspecs/windows_protocols/ms-authsod/ms-authsod_files/image027.png)
