IAM makes it easier for you to manage permissions for AWS services accessing your resources | AWS Security Blog

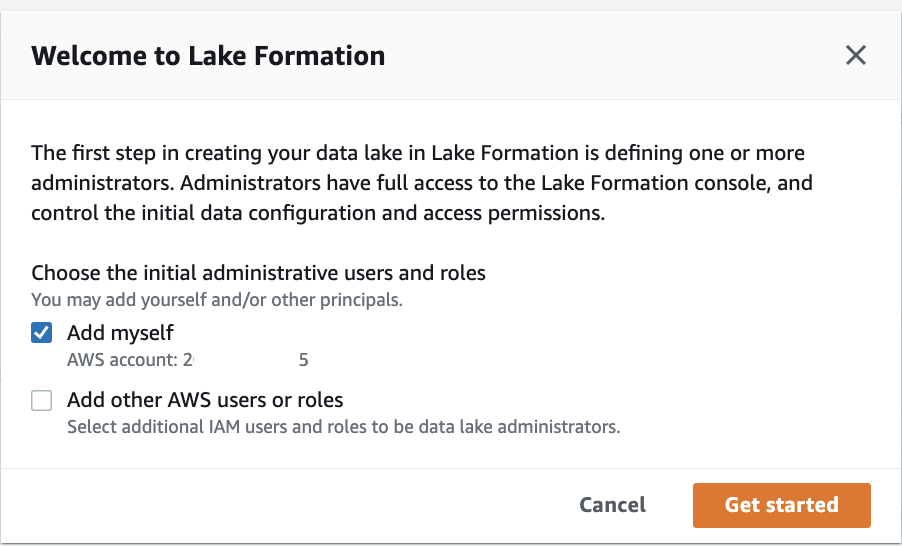
Enable cross-account access for Amazon SageMaker Data Wrangler using AWS Lake Formation | AWS Machine Learning Blog
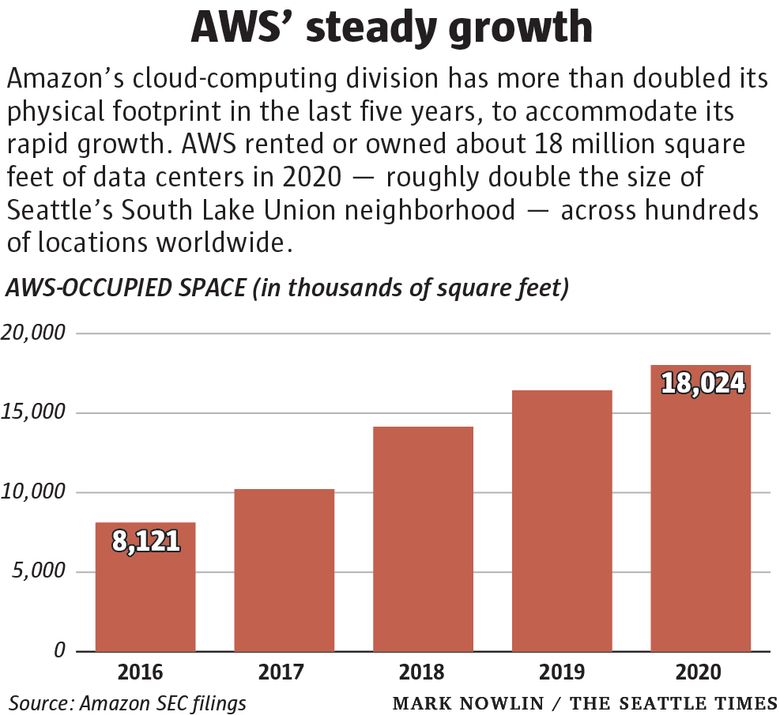
In the 15 years since its launch, Amazon Web Services transformed how companies do business | The Seattle Times
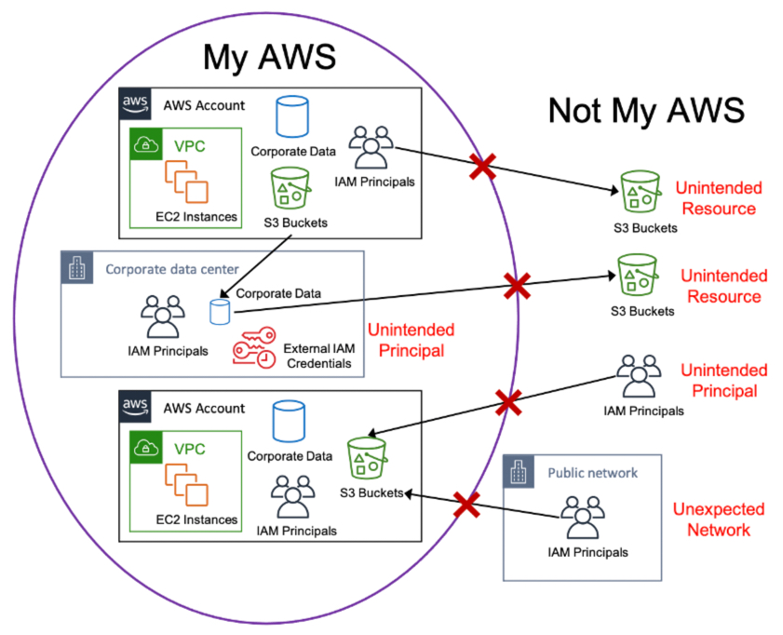
Jeff Barr ☁️ (@ 🏠 ) 💉 on Twitter: "#AWS for Industries: Using AWS Services to Protect Against, Detect, and Respond to Unauthorized Data Access - https://t.co/gWdsSdIgM8 The intent is to design

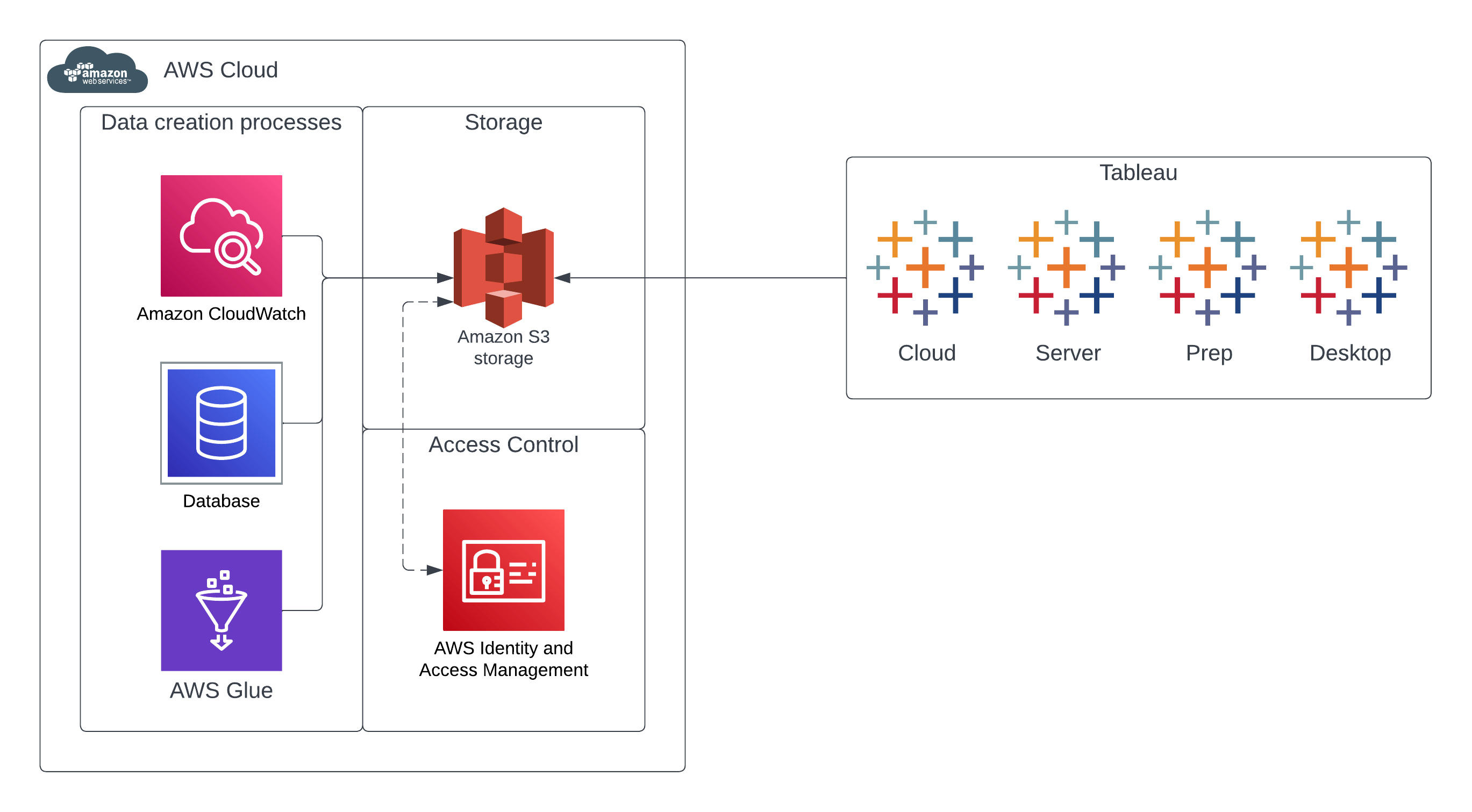
Controlling data lake access across multiple AWS accounts using AWS Lake Formation | AWS Big Data Blog

Access and manage data from multiple accounts from a central AWS Lake Formation account | AWS Big Data Blog